Security
Authentication
Every user has to authenticate themselves before using Airflow and there are several ways of doing this.
Webinterface
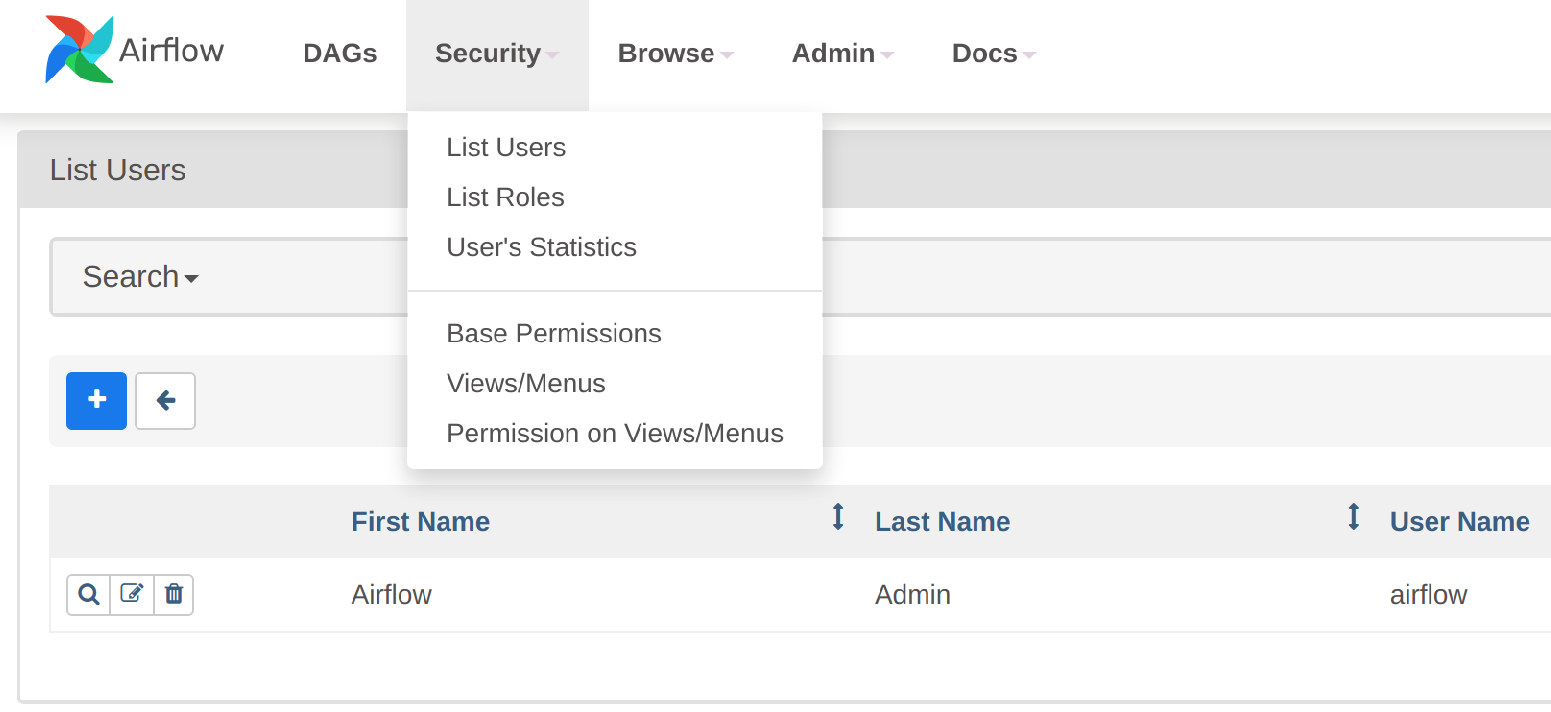
The default setting is to view and manually set up users via the Webserver UI. Note the blue "+" button where users can be added directly:
LDAP
Airflow supports authentication of users against an LDAP server. This requires setting up an AuthenticationClass for the LDAP server. The AuthenticationClass is then referenced in the AirflowCluster resource as follows:
apiVersion: airflow.stackable.tech/v1alpha1
kind: AirflowCluster
metadata:
name: airflow-with-ldap
spec:
image:
productVersion: 2.9.3
clusterConfig:
authentication:
- authenticationClass: ldap (1)
userRegistrationRole: Admin (2)| 1 | The reference to an AuthenticationClass called ldap |
| 2 | The default role that all users are assigned to |
Users that log in with LDAP are assigned to a default Role which is specified with the userRegistrationRole property.
You can follow the Authentication with OpenLDAP tutorial to learn how to set up an AuthenticationClass for an LDAP server, as well as consulting the AuthenticationClass reference .
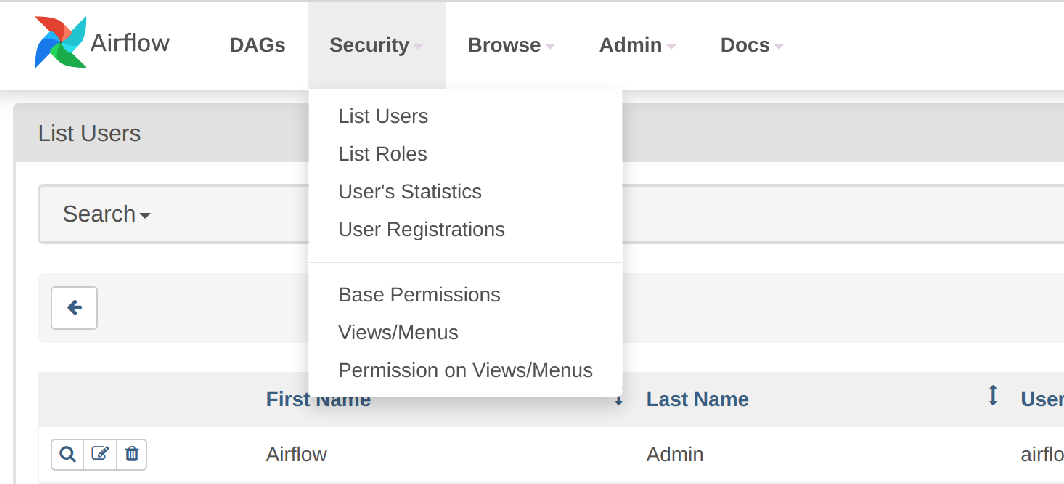
The users and roles can be viewed as before in the Webserver UI, but note that the blue "+" button is not available when authenticating against LDAP:
Authorization
The Airflow Webserver delegates the handling of user access control to Flask AppBuilder.
Webinterface
You can view, add to, and assign the roles displayed in the Airflow Webserver UI to existing users.
LDAP
Airflow supports assigning Roles to users based on their LDAP group membership, though this is not yet supported by the Stackable operator.
All the users logging in via LDAP get assigned to the same role which you can configure via the attribute authenticationConfig.userRegistrationRole on the AirflowCluster object:
apiVersion: airflow.stackable.tech/v1alpha1
kind: AirflowCluster
metadata:
name: airflow-with-ldap
spec:
clusterConfig:
authentication:
- authenticationClass: ldap (1)
userRegistrationRole: Admin (2)| 1 | The reference to an AuthenticationClass called ldap |
| 2 | All users are assigned to the Admin role |